Configure readers for AES authentication and encryption
Setting up AES authentication and encryption involves 2 steps: (1) configure the reader (this page), then (2) establish the authenticated connection in your host application.
To configure the reader, add the AES Authentication and Encryption component to the reader configuration and define security levels.
Add AES Authentication and Encryption component
As this component is only relevant in few projects, it is not included in ConfigEditor by default, but needs to be added manually.
The component Security Settings (BRP Communication) included in ConfigEditor versions below 4.26
must no longer be used due to a known bug.
To add AES Authentication and Encryption:
-
This component does not work with Ethernet readers. If you want to use AES with Ethernet readers, we provide an adapted component on request.
-
Open the latest version of BALTECH ConfigEditor.
Download it here as part of BALTECH ToolSuite. -
Open the BALCFG file of your existing configuration.
If you don't have a configuration file yet, create a new one. -
Click the Plus icon > Import... to import the downloaded component.
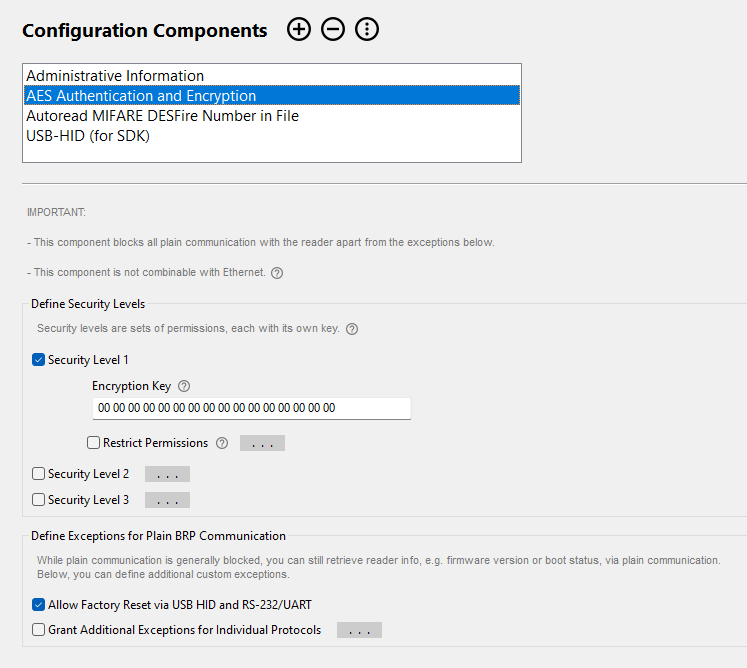
Define security levels
Define up to 3 security levels, each with its own key and permissions.
To define the first security level:
- Make sure Security Level 1 is enabled.
- In the Encryption Key field, enter an AES 128-bit key, expressed as a hexadecimal string with 32 characters.
-
By default, full permissions are assigned to this security level. To exclude permissions, enable Restrict Permissions and deselect them.
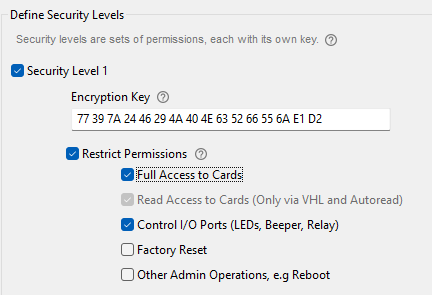
To define additional security level:
If you need several security levels because you have multiple host applications that you want to grant individual permissions, repeat the above steps accordingly.
Each security level is defined individually, i.e. permissions you want to assign to multiple levels must be explicitly added to each of them. An exception is level 3: It is automatically assigned full permissions.
Create exceptions for plain communication
While plain communication is generally blocked, you can still retrieve reader info, e.g. firmware version or boot status, via plain communication. In addition, you can define custom exceptions.
Factory Reset
By default, the exception Allow Factory Reset via USB HID and RS-232/UART is enabled. We highly recommend you keep it enabled, so you can easily reset the reader in case of misconfiguration.
If you disable this exception, you need to assign the Factory Reset permission to at least 1 security level.
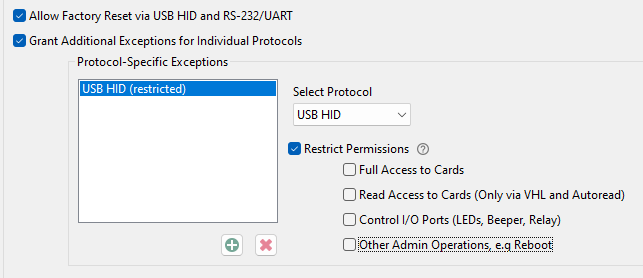
Additional Exceptions
Apart from factory reset, you can grant additional host-protocol-specific exceptions. For example, you may want to allow admin operations such as reboot via the USB HID maintenance interface.
To add additional exceptions:
- Enable Grant Additional Exceptions for Individual Protocols.
- In the drop-down, select the interface for which you want to create an exception, e.g. USB HID.
- By default, full permissions will be granted for plain communication via this protocol. To exclude permissions, enable Restrict Permissions and deselect them.
-
To add an exception for another protocol, click
 .
. 
That's it. In your host application, you need to specify the number and encryption key of the respective security level when establishing an authenticated and encrypted connection.